AWS's Ubuntu image gets bootstrapped with your credentials being added to a user called ubuntu. After the machine comes up, you can SSH into your new box with the ubuntu user.
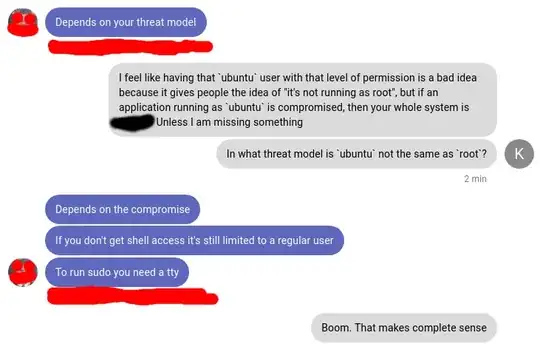
This user is a sudoer, and based on the sudoers file, this user can do pretty much anything that root can, as long as you preface a command with sudo, without any password being entered. This negates some of the benefits of sudo because there is no interactive password prompt. As far as I can tell, this also pretty much means that you should never run public-facing applications as this user, because if someone could find a way to execute shell commands via your application, they could take control of your system.
My real question is: why does this user exist? Why not just grant SSH access to the root account, with the expectations that someone would create unprivileged accounts to run an app? Doesn't having this ubuntu user just add confusion? I could see someone thinking "my systemd application isn't running as root, it's running as ubuntu, so I am safe".
Am I missing some purpose of this kind of user, which is not root, but is a passwordless sudoer?
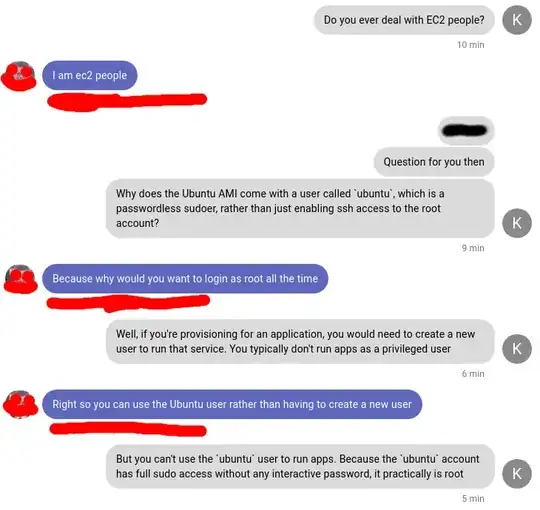
ubuntuuser can use sudo without entering a password (because that user does not have a password) – kbuilds Nov 29 '18 at 22:16passwdon that user... – Fabby Nov 29 '18 at 22:26passwdthat user to set the password, then also modify the sudoers file to disable passwordless sudo access. But the point here is what is the main difference between a passwordless sudoer and the root account itself? – kbuilds Nov 29 '18 at 22:29